For years, organizations have worried about phishing, ransomware, and supply‑chain compromises. But a quieter, more insidious threat has been growing in parallel: North Korean IT workers pose as legitimate remote developers, slipping into Western companies under fabricated identities, and funneling earnings and access back to the Democratic People’s Republic of Korea (DPRK) regime.
This isn’t a hypothetical risk. Recent law‑enforcement actions and investigations show a sprawling ecosystem of synthetic identities, rented accounts, and polished fake résumés, all designed to pass as contractors or normal remote workers for the express purpose of penetrating companies in the cryptocurrency markets.
The ecosystem is complex, effective, and organized. There are broad indicators organizations need to watch out for and specific countermeasures needed to mitigate the risk.
Key Takeaways
- North Korean IT workers are posing as legitimate remote developers using fabricated identities to infiltrate Western companies in the cryptocurrency sector.
- These actors leverage sophisticated methods, including synthetic identities and AI-generated documents, to bypass traditional hiring and identity verification systems, often with help from external parties.
- Organizations need to enhance worker identity verification processes, implementing processes to identify red flags in applicant résumés, geolocation inconsistencies, and unusual login behaviors.
Understanding the DPRK Remote IT Threat Landscape
North Korean IT workers operating abroad in remote countries have one major challenge: they cannot use their real identities. To work for Western companies, they typically choose to appear as freelancers from Canada, Japan, China, Eastern Europe, or the U.S.
To do that, they build or acquire synthetic personas across:
- Professional networking sites
- Gig‑economy platforms
- Developer communities
- Code‑challenge and skills‑testing sites
- Payment processors
- Cloud and developer tool ecosystems
A prior investigation highlights this threat as the computer accounts were infected with malware from a single DPRK‑linked email registering across dozens of platforms, including GitHub, job boards, and cloud services, creating the illusion of a legitimate, well‑established professional.
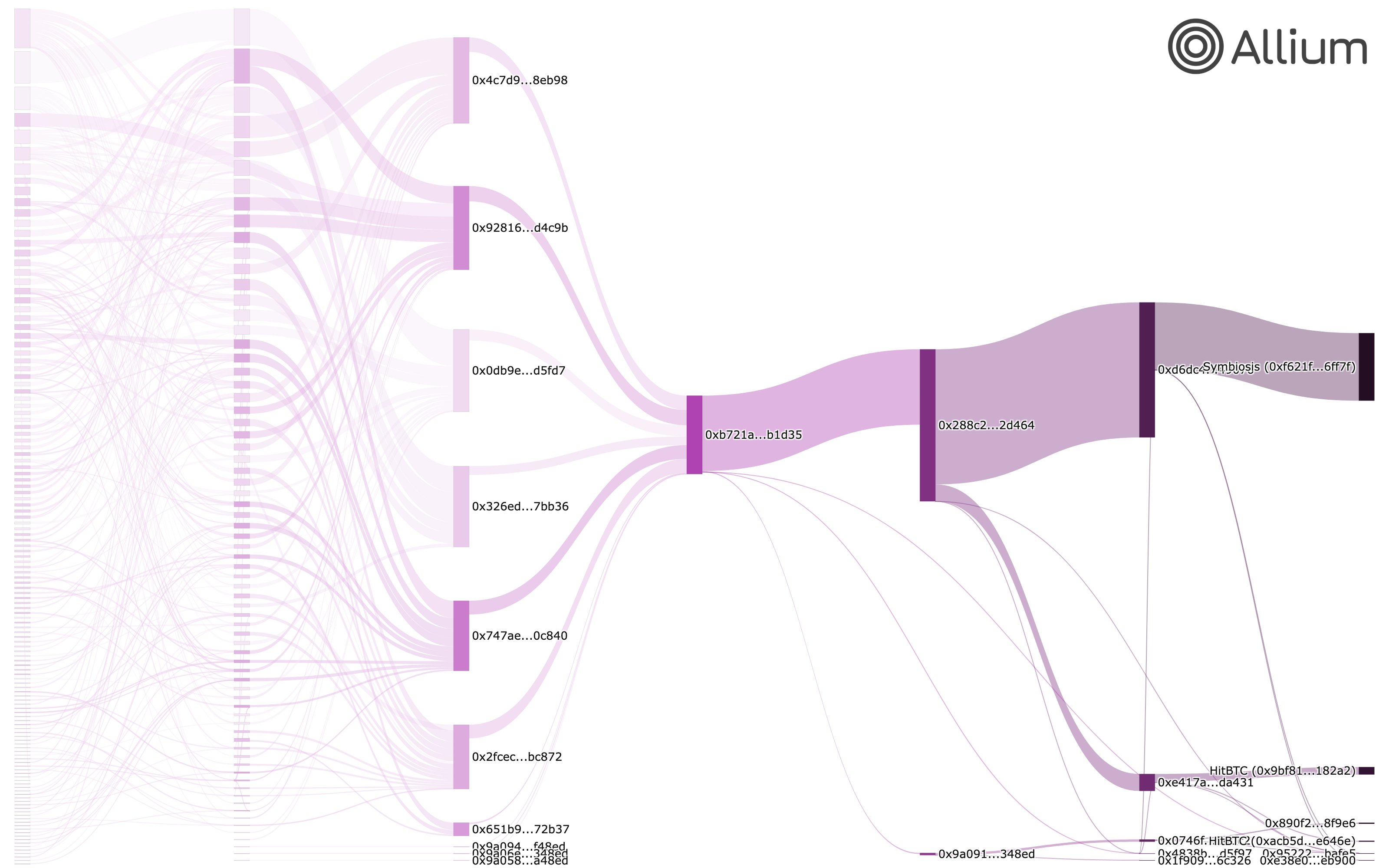
Using Allium’s on-chain analytics platform, North Korean IT workers who infiltrated approximately 25 crypto projects were traced as laundering salary payments through a structured seven-layer pipeline. Funds were routed from 131 source addresses through DeFi protocols, no-KYC exchanges, and cross-chain bridges into a single DPRK-controlled hub wallet before exiting via Symbiosis Finance and HitBTC.
Despite the complexity, all funds ultimately passed through a single chokepoint address, meaning a single sanctions designation could have disrupted the entire operation. This analysis represents one consolidation hub within the broader DPRK IT worker campaign.
The Rise of Synthetic Identities and Their Impact on Hiring
DPRK workers don’t just create fake identities; they buy or rent real ones as well. In some instances, external parties are complicit in this fraudulent worker scheme.
“The DPRK has continued to innovate its approach to placing IT workers in tech companies,” said our affiliate, Security Alliance. “Today, IT workers create sophisticated personas to not only target the companies directly, but also to recruit unsuspecting accomplices as facilitators. These facilitators then act as the point of contact for future interactions, making detection significantly more difficult. Once embedded within a company, IT workers can then leverage their trusted position to recruit additional workers, resulting in a deeply embedded threat actor that is extremely difficult to remove.”
Common examples include, but are not limited to:
- Individuals selling their Upwork or Freelancer accounts
- People renting out verified accounts for a monthly fee
- Sellers offering “full access” accounts with payment systems attached
- Buyers explicitly seeking accounts from certain countries
This market exists because gig‑economy platforms are gatekeepers. A verified account with a clean history is a golden ticket. DPRK workers use these accounts to:
- Bid on jobs
- Pass identity checks
- Receive payments
- Build a work history under someone else’s name
Because of this, recent Department of Justice (DOJ) cases have included U.S. citizens arrested for providing material support, helping commit identity fraud against U.S. persons or knowingly renting out their own identities to DPRK workers.
The Role of AI in Criminal Activities: Generating IDs and Résumés
AI tools have accelerated other parts of this criminal ecosystem through AI-generated identity documents.
Underground services now produce photorealistic driver’s licenses and passports using neural networks. Forged digital identity documents, along with Virtual Private Networks (VPNs) and proxy internet networks, help remote workers pass traditional know your customer (KYC) Human Resource checks on freelance and enterprise hiring platforms, highlighting weaknesses in current applicant screening systems.
To detect fraudulent professionals, organizations should know what to look for on résumés. Historically, DPRK workers often use the same language on résumés, including:
- Job descriptions
- Blockchain‑project narratives
- ”8+ years of experience” claims
- “Full-stack developer” skills description
- Copy‑pasted bullet points
A Practical Example
Let’s say, a DPRK résumé included the unique string, “Contributed to one of the biggest mining pools on the AION network”. By taking this string to a Google search, it might appear across dozens of unrelated profiles. Due diligence is key here, and organizations should vet résumés appropriately to avoid bad-faith actors. The vetting needs to mimic what the banking world does to validate the digital elements provided before online banking is enabled. KYE and KYC are synonymous and need to be more than confirming elements of a resume.
Another red flag is reusing the names and photos of real people, including mid-tier athletes and academic professionals who have nothing to do with software development. Many believe this is used to make the developer’s limited online presence show up after page two or three of search results, frustrating and unlikely HR investigation.
Understanding the Risk and Strategies to Identify
Hiring a DPRK IT worker isn’t just a compliance issue — it’s a looming security threat. These workers may exfiltrate source codes, install backdoors, steal credentials, funnel earnings, or even provide access to internal systems to more sophisticated DPRK units. There have been instances where DPRK operators embedded malicious code into trusted developer tools. This serves as an important reminder that developer access is one of the most dangerous access levels in any organization.
The DPRK remote worker risk is obvious, but strategies to detect malicious applicants or employees may be more challenging. Below are the most reliable red flags warranting further investigation:
Identity & Behavior Signs
- Résumés with distinct phrasing that can be cross-referenced to dozens of candidate profiles via simple internet searches
- Overly broad skillsets (AI, blockchain, mobile, backend, DevOps — all in one)
- Geolocation inconsistencies between the applicant’s IP address, résumé location, and hardware shipping address
- Recently created email addresses with no history of compromise
- Use of Western‑sounding names with mismatched cultural details
Technical Signals
- Logins from Hong Kong or Russian proxy networks
- VPN endpoints associated with known DPRK activity
- GitHub commits with scrubbed commit metadata (admittedly, some Westerners use this out of concern for privacy)
Securing Your Organization with EisnerAmper
The synthetic‑identity ecosystem supporting DPRK IT workers is sophisticated, global, and constantly adapting. Remote work has become normalized when sourcing high-skilled talent, reducing the barrier to entry for these actors.
Organizations must treat remote‑worker identity verification as a security control, not an HR formality. The cost of getting it wrong isn’t just financial; it’s the risk of handing your source code, infrastructure, customer data, or financial capital to one of the most aggressive adversaries in the world.
EisnerAmper can help you evaluate and improve the resilience of your Insider Risk Management Program, HR, and Supply Chain Risk Management programs to mitigate and combat this growing problem.















